|
Enterprise information security architecture
Enterprise information security architecture is the practice of designing, constructing and maintaining information security strategies and policies in enterprise organisations. A subset of enterprise architecture, information security frameworks are often given their own dedicated resources in larger organisations and are therefore significantly more complex and robust than in small and medium-sized enterprises. OverviewEnterprise information security architecture is becoming a common practice within financial institutions around the globe. The primary purpose of creating an enterprise information security architecture is to ensure that business strategy and IT security are aligned.[1] Enterprise information security architecture topics Enterprise information security architecture was first formally positioned by Gartner in their whitepaper called “Incorporating Security into the Enterprise Architecture Process”.[2] High-level security architecture framework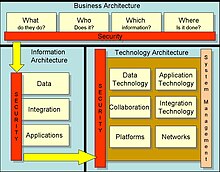 Whilst security architecture frameworks are often custom designed in enterprise organisations, several models are commonly used and adapted to the individual requirements of the organisation Commonly used frameworks include:
See alsoReferences
Further reading
|
Portal di Ensiklopedia Dunia